
Safe & Sound TShirt — Mercury Stardust
Mercury is a hacking tool used to collect information and use the information to further hurt the target - 4n6strider/Mercury. Skip to content. Toggle navigation. Sign in Product Actions. Automate any workflow Packages. Host and manage packages Security. Find and fix vulnerabilities.

MACETE PARA LIGAR MOTORZINHO MERCURY!!!HACK TO TURN ON THE MERCURY
The ransomware gang claimed an attack on the NZ-based MSP earlier this month, and now may have launched a supply chain attack. A ransomware attack by cybercrime gang LockBit 3.0 on New Zealand-based managed service provider Mercury IT appears to have led to numerous organisations from NZ appearing on the gang's dark web victim blog.
Lost data stock vector. Illustration of computer, personal 1182516
Located in Auckland, Wellington, Hamilton and Melbourne, Mercury IT manages IT services for more than 3000 users and around 200 organisations, according to its website. "While work is underway to understand and respond to this particular incident we have some key messages for individuals, organisations and members of the public in general.

'Former staff' claim abuse by exRep. Hill in Twitter hack house abuse
April 2023 update - Microsoft Threat Intelligence has shifted to a new threat actor naming taxonomy aligned around the theme of weather.MERCURY is now tracked as Mango Sandstorm and DEV-1084 is now tracked as Storm-1084.. To learn more about the new taxonomy represents the origin, unique traits, and impact of threat actors, to get complete mapping of threat actor names, read this blog.

Mercury Hacks YouTube
Microsoft labels Iranian-affiliated attackers as "Mercury." This group initiated the network access, apparently via Log4j vulnerabilities, and then handed off operations to a "DarkBit persona.

History Hack
Accuro is the latest provider to be hit after a string of cyber-attacks that included a hack on central North Island provider Pinnacle Midlands Health Network in October and the earlier ransomware.
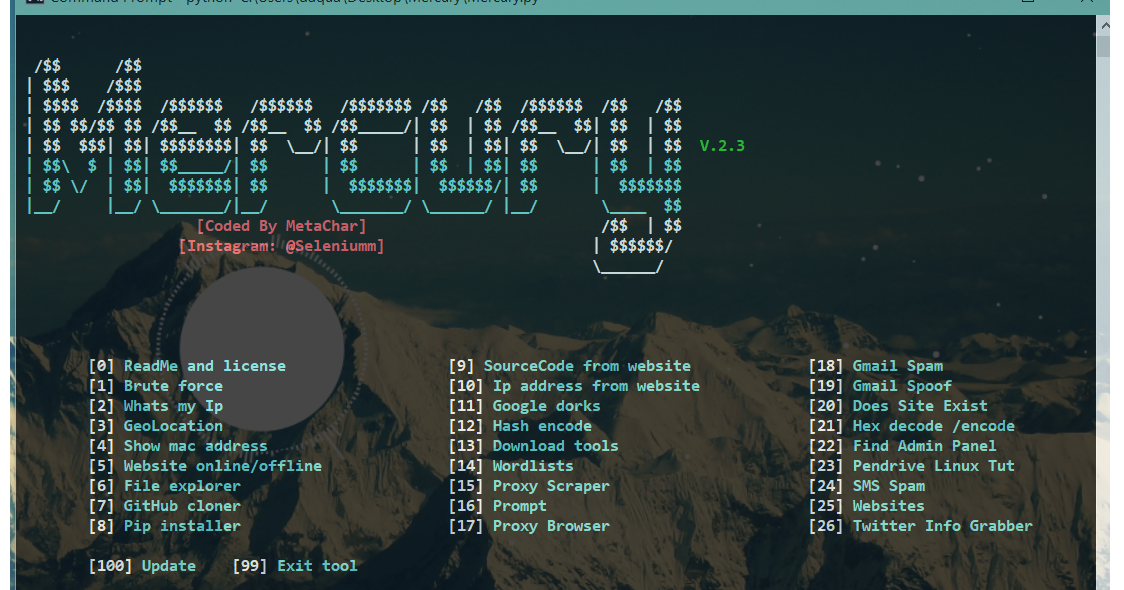
Mercury A Hacking Tool Used To Collect Information And Use The
November 2023. Mercury-hack has no activity yet for this period. Show more activity. Seeing something unexpected? Take a look at the GitHub profile guide . GitHub is where Mercury-hack builds software.

MERCURY HACK WAR ROBOTS YouTube
The personal information of "potentially" 3.5 million people was compromised by an "international software hack" of Oregon's Department of Motor Vehicles, according to ODOT.
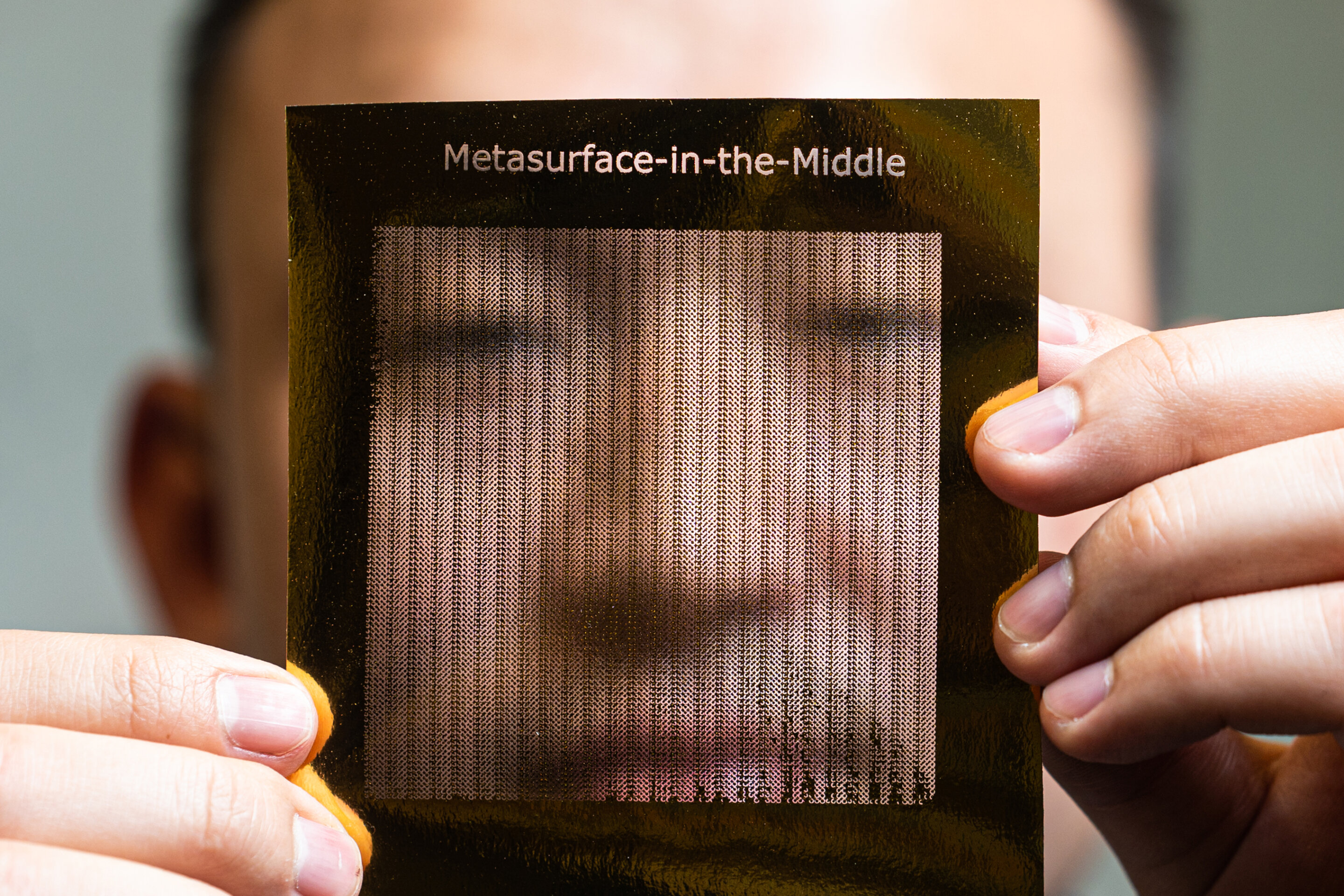
Eavesdroppers can hack 6G frequency with DIY metasurface Trendradars
Brunswick Corporation calls itself the global leader in marine recreation and is home to 60 industry-leading brands, including Mercury Marine, which specializes in boat engines and propellers.
Как разблокировать телефон, если забыл пароль, пин или графический ключ
Features BruteForce Mercury uses Selenium to automatically input passwords into a website GeoLocation Gelocation allows the user to pin point the exact location of the ip address Sms Spam Uses gmail to spam sms Spoof Email Sends anonymous emails Check If Website Exists Mercury checks if the website is real Check if Website Is Down Checks if.

Keyboard comeback BlackBerry Mercury launch set for next month TechRadar
As tipster [BrightBlueJim] wrote us, this project has everything: high vacuum, home-made torch glassware, and large quantities of toxic heavy metals. (Somehow [Jim] missed out on the high-voltage.
AVAKIN Life Hack.pdf DocDroid
There's no need to "remove" the root/hack -- if you boot the device without a SD card (or scripts) it should work normally, just without the root/customizations. This is a very slow device so it is normal to hear the start up sound 2 times (one for ppsapp from the flash and one from the modified one in SD card).

THE GREAT HACK DOC NYC
April 2023 update - Microsoft Threat Intelligence has shifted to a new threat actor naming taxonomy aligned around the theme of weather.MERCURY is now tracked as Mango Sandstorm.. To learn about how the new taxonomy represents the origin, unique traits, and impact of threat actors, and to get a complete mapping of threat actor names, read this blog: Microsoft shifts to a new threat actor.

Cabo Comando Motor Popa Mercury Mariner 1114 Pés Geração 1 UFLEX
Mercury Security has been informed of a firmware security issue affecting the following hardware: LP1501, LP1502, LP2500, LP4502, and EP4502. This issue makes it possible for a hacker to have a level of access to these controllers. This is done through the Web Browser that accesses and configures Mercury controllers.

War Robots SUPER THANOS Mercury Hack YouTube
There is a folder mercury_proj and below are the contents of this folder : In the notes.txt file we have two accounts with encrypted passwords, one is webmaster, the other is linuxmaster. We can.
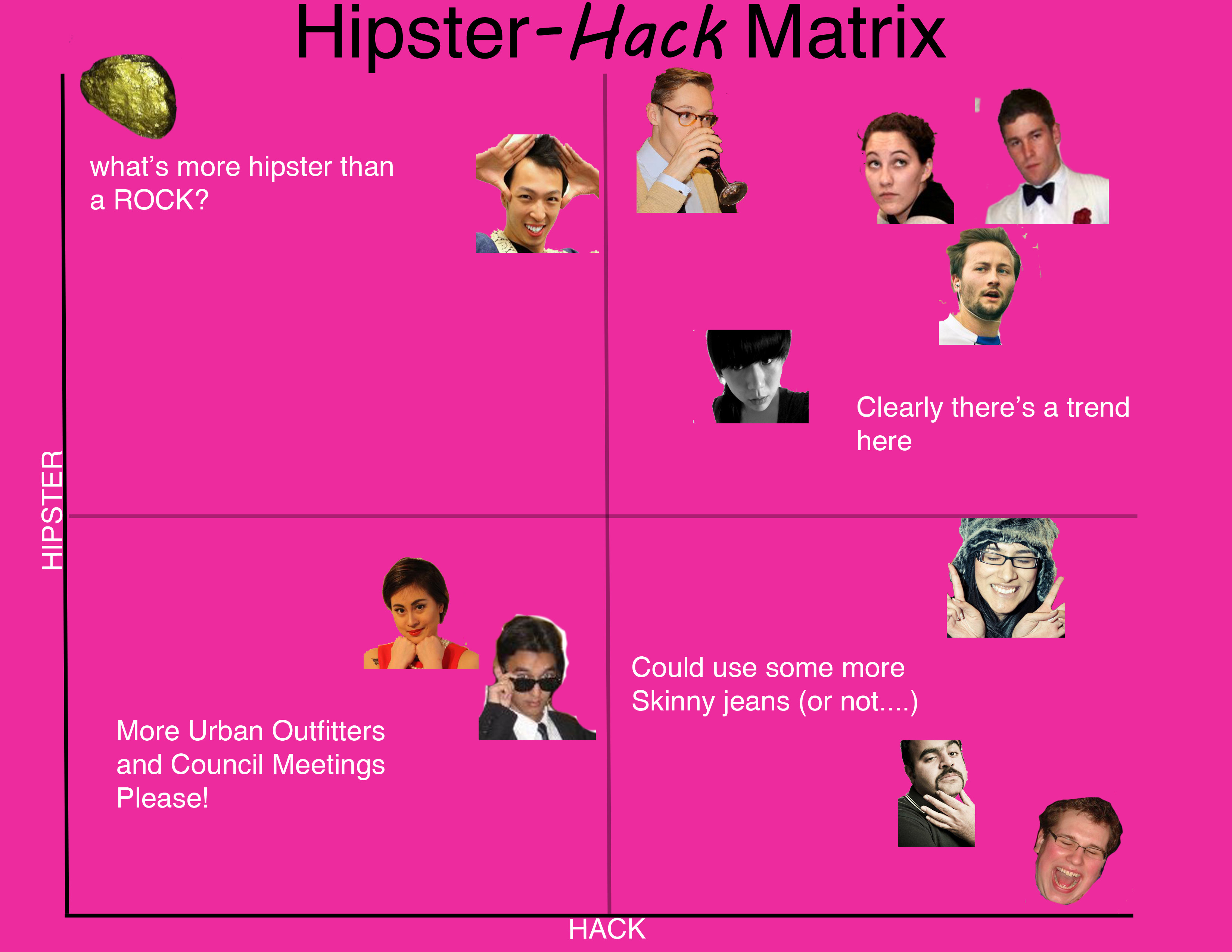
hipster hack scale AMS Confidential
Critical Mercury Security Vulnerabilities. HID's Mercury Security has 8 vulnerabilities, including the highest possible 10.0 risk, and researchers recently demonstrated how to hack open a door while using one of the industry's biggest brands. In this report, IPVM examines the vulnerabilities, exposed by researchers from a US cybersecurity firm.